The hallmark of the Visory experience, our dedicated team of professionals provides a high degree of support for all your IT needs
Leading edge solutions that are always working to maintain the integrity of your firm’s IT backbone
Best in class security to protect your firm’s data and technology
Tips, advice, and industry insight from our team of accountants and business owners to yours.
Take your business to new heights with Visory’s flexible QuickBooks hosting solutions
The same Sage you work in every day, only better
An affordable CRM for small- and medium-sized businesses, built to support your sales, marketing and customer service needs
Revolutionize your next tax season with added efficiency and mobility
Access critical applications that are integrated seamlessly into your workflow, conveniently hosted on the same server
Access affordable enterprise-grade hosting solutions with none of the IT burden

Our dedicated professionals can be your outsourced IT team, so your internal resources don’t have to bear the burden of uptime alone.
We’ll help you develop and implement the right cybersecurity policies and protocols to keep your firm secure and in compliance with regulatory guidance
We’re here to manage your firm’s IT activity, safeguarding the integrity of your infrastructure and devices, so you don’t have to
We’ll manage your cybersecurity policies and protocols to keep your firm secure and in compliance
Security that ensures everyone granted access is who they claim to be
Educate and train your most important last line of defense – your people
Protection where people and their machines intersect
Secure access to your data. Reduce the risk of compromise, prevent cyberthreats.
A different approach to protecting emails
Secure single sign-on access for a connected world
Backup your data for business continuity and compliance
Keep everyone on the same page. Any user, every device.
Secure connections for all your users, devices and networks
Get started on a robust security plan with a WISP for your business
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource

IRS 4557 and the FTC Safeguards Rule
Complying with state and federal privacy regulations and more
Get started on a robust security plan with a WISP for your business
Educate and train your most important last line of defense — your people.
Protect your organization with the expertise of our Chief Information Security Officers (CISO) without having to hire a full-time resource
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Lorem ipsum dolor sit amet, consetetur sadipscing elitr, sed diam nonumy
Cybersecurity awareness tips aren’t just IT best practices — they’re a business survival strategy. Nearly 60% of small businesses close within six months of a data breach.
Beyond financial loss, a breach can also cause regulatory fines, reputational damage, and permanent loss of customer trust. For many small businesses, even a single incident can take years to recover from — if recovery happens at all.
As a business leader, protecting sensitive data, preventing fraud, and maintaining client trust is critical. The challenge? Cyber threats are evolving every day, and most organizations don’t have the budget to hire a full-time cybersecurity engineer.
But here’s the good news: you don’t have to figure it all out alone. With the right cybersecurity services, your firm can access enterprise-level protection without the cost of hiring a dedicated cybersecurity engineer.
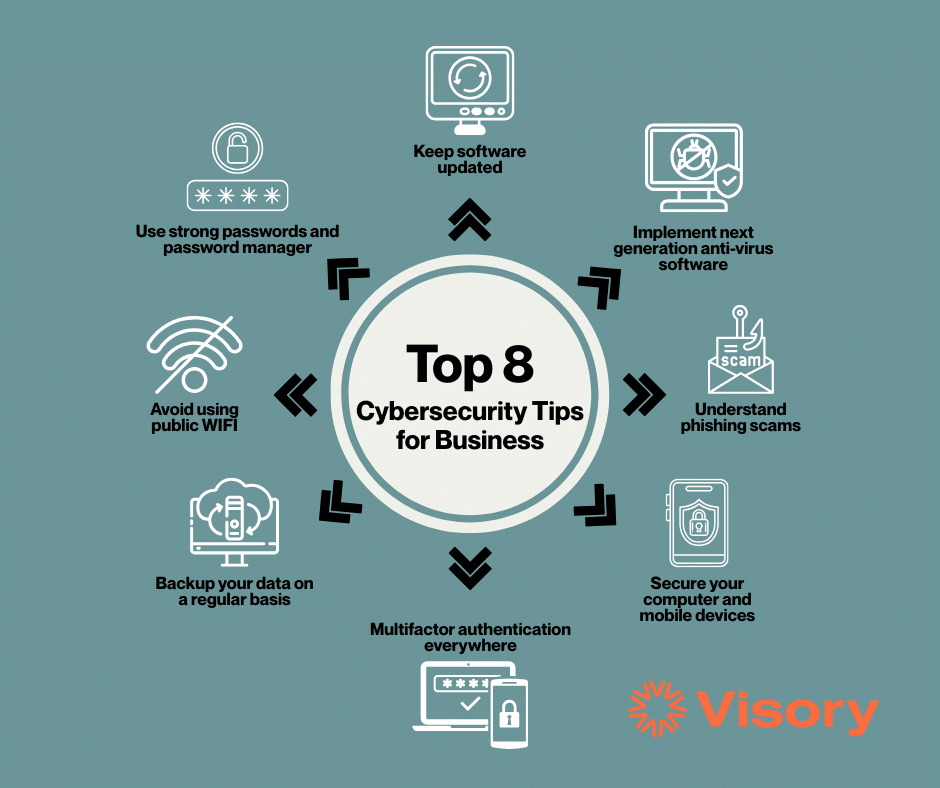
8 Cybersecurity Awareness Tips Every Business Must Know
1. Keep Software Updated
Outdated systems are open doors for hackers. Even one missed patch can lead to ransomware shutting down operations during your busiest season.
2. Implement Next-Generation Antivirus
Traditional antivirus often misses today’s advanced threats. Next-gen endpoint protection detects and blocks attackers before they spread across your network.
3. Understand Phishing Scams
Most breaches start with a single email click. A spoofed message from a government agency, vendor, or bank could leak financial records, trigger wire fraud, or destroy customer trust.
4. Secure Computers and Mobile Devices
Laptops, tablets, and phones store sensitive information but are often left unprotected. Without encryption or monitoring, a stolen device can mean total data loss.
5. Use Multifactor Authentication (MFA)
Passwords are easily guessed, stolen, or sold on the dark web. MFA blocks 99% of account takeovers and is one of the simplest cybersecurity awareness tips you can implement.
6. Backup Your Data Regularly
No backups = no recovery. Ransomware has forced many businesses to halt operations entirely because they couldn’t restore their files.
7. Avoid Using Public Wi-Fi
Public Wi-Fi networks are hunting grounds for cybercriminals. Logging in at a coffee shop could expose bank records, contracts, and client credentials.
8. Use Strong Passwords and a Password Manager
Daisy123 might be easy to remember, but it’s also easy to hack. Weak passwords lead directly to breaches; managers simplify secure habits without slowing teams down.
Why Cybersecurity Awareness Tips Matter for Your Business
👉 Cyberattacks don’t just disrupt operations — they threaten trust, compliance, and survival.
👉 Business owners should stay focused on growing their companies, not on managing evolving cyber threats.
That’s why so many businesses turn to managed cybersecurity services:
- Enterprise-level protection without the cost of a full-time engineer
- 24/7 monitoring and incident response
- Compliance with IRS, FTC, and state requirements
- Reduced liability and stronger client confidence
Ready to Act on These Cybersecurity Awareness Tips?
Take the first step toward smarter cybersecurity. Fill out the form below to:
✅ Schedule a free consultation
✅ Get a personalized security risk review
✅ Learn how to secure your firm with cost-effective, enterprise-grade protection
Cyber threats are not slowing down — attackers grow more sophisticated every year, and businesses that delay action often find themselves responding to a breach rather than preventing one.
You don’t have to do this alone. Partnering with experts ensures you always have enterprise-grade defenses, a clear plan of action, and proactive protection that evolves as threats evolve.
The best time to strengthen your defenses was yesterday. The next best time is today.



